In the digital age, the parallel between biology and technology has never been more apt. For decades, cybersecurity relied on fortress mentalities: building higher walls and deeper moats to keep invaders out. However, as cyber threats evolve at machine speed and adversaries begin to wield artificial intelligence as a weapon, static defenses are crumbling. The future of cyber resilience lies not in rigid fortifications, but in a dynamic, adaptive, and autonomous defense mechanism an AI-driven Digital Immune System.
Just as the human body uses a complex, layered immune response to fight off pathogens it has never seen, a digital immune system leverages artificial intelligence to predict, detect, and neutralize cyber threats in real-time. This concept represents a paradigm shift from reactive “break-fix” security to proactive “predict-prevent” resilience. This article explores how AI is being woven into the fabric of our networks to create a self-healing, adaptive defense layer capable of outpacing modern digital pathogens .
The Biological Blueprint: Learning from the Body
To understand the digital immune system, we must first appreciate its biological counterpart. The human immune system is a masterpiece of distributed intelligence. It doesn’t rely on a central brain to tell it when a toe is infected. Instead, it uses a series of localized responses: pattern recognition to identify familiar threats, adaptive immunity to learn from new invaders, and memory cells to ensure a faster response next time .
Traditional Security Operations Centers (SOCs) function like an allergic reaction rather than a healthy immune system. They are inundated with false positive alerts, causing “alert fatigue” and wasting human talent on mundane tasks. When a real breach occurs, the response is often too slow because it requires human intervention at every stage.
AI transforms this dynamic. By embedding machine learning models directly into the network fabric an approach known as “AI at the edge” systems can process information locally, reducing latency and making millisecond-level decisions . This mirrors how our autonomic nervous system handles reflex arcs without consulting the brain, allowing for immediate action against threats.
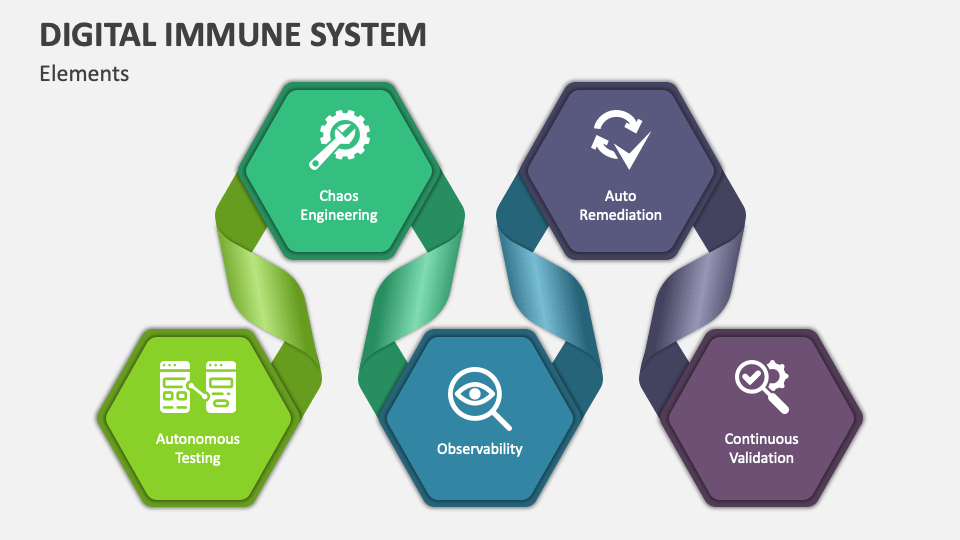
The Core Components of a Digital Immune System
Building a robust digital immune system requires more than just installing a smart firewall. It requires a holistic architecture that spans the entire digital ecosystem, from development pipelines to runtime environments. Here are the essential components, structured to mimic biological immunity.
A. Proactive Hygiene and Posture Management (The Adaptive Immune System)
Before fighting an infection, the body maintains baseline health. In digital terms, this involves understanding your “genetic makeup” a complete inventory of all devices, data flows, and AI models within the organization. Automated scanning tools must be integrated into development pipelines to scan open-source models (like those from Hugging Face) for embedded malware or signs of “model poisoning.” This ensures that vulnerabilities are not introduced during the development phase, maintaining a “healthy lifestyle” for the digital ecosystem .
B. AI Red Teaming and Controlled Exposure (Vaccination)
Immunity is strengthened through controlled exposure to weakened pathogens. Similarly, digital systems must undergo rigorous AI Red Teaming. Using frameworks like the OWASP Top 10 for Large Language Models (LLMs), organizations can simulate attacks such as prompt injection or data leakage. This “training ground” allows the AI to encounter threats in a safe environment, learning to recognize and reject malicious inputs without exposing critical data .
C. Runtime Protection and Autonomous Response (The Immune Response)
When a pathogen breaches the skin, the body’s innate immune system rushes to the site. In cybersecurity, this is runtime protection. AI models embedded in the network analyze traffic patterns, user behavior, and system calls. If an autonomous agent say, a customer service chatbot suddenly attempts to access a sensitive financial database, the digital immune system recognizes this anomalous behavior. It can then enforce the “principle of least privilege” by automatically revoking the agent’s access or sandboxing it to prevent lateral movement, effectively neutralizing the threat from within .
Defensive AI: The Third Pillar of National Security
Beyond the enterprise, the concept of a digital immune system is gaining traction as a matter of national security. Historically, policy responses to AI threats have focused on two pillars: containment (export controls on chips) and alignment (ethical guardrails). However, these are insufficient against adversaries who use open-source models and sanction-dodging hardware .
This has given rise to a third pillar: Defensive AI. This involves building purpose-built AI models to monitor, detect, and respond to anomalies across critical infrastructure. The Bulletin of the Atomic Scientists argues that just as we developed antibiotics to fight bacteria, we need AI-native defenses to fight malicious AI . These systems act as a “nerve layer” for the grid, capable of flagging silent code execution at a power substation before physical damage occurs. In biosecurity, defensive AI acts as a digital sentinel within DNA synthesis pipelines, screening orders for pathogen fragments and halting production if a “toxin gene” is detected .
Bio-Inspired Algorithms in Practice
The technical implementation of these systems often relies on Artificial Immune Systems (AIS) . These are algorithms inspired by the theoretical immunology of the human body. They are particularly suited for the dynamic and distributed nature of cloud and edge computing .
-
Negative Selection Algorithms: Modeled on how the body distinguishes self from non-self. The AI is trained on “normal” network behavior and is designed to detect deviations (non-self) that could indicate an intrusion.
-
Dendritic Cell Algorithms: Inspired by the behavior of dendritic cells in the human body, which process danger signals. In cybersecurity, these algorithms correlate multiple data points to determine the context of an anomaly, reducing false positives by understanding the “danger context” of a network event .
These algorithms are lightweight enough to run on IoT devices, enabling security at the very edge of the network where traditional antivirus software cannot operate .
The Quantum Conundrum and Future Threats
Looking toward the future, the digital immune system must evolve to face threats that are currently unimaginable. By 2050, we may face “Ransomware 3.0,” where attackers don’t just lock files but threaten to lock your digital twin or connected car. The defense against this will require predictive orchestration powered by real-time data streams .
Furthermore, the rise of quantum computing poses an existential threat to current encryption standards. A quantum computer could break today’s strongest security protocols in minutes. Here, the digital immune system of the future will rely on post-quantum cryptography and quantum-safe algorithms. The system’s “digital intuition” its ability to assess incomplete data and interpret intent will be crucial in a world where deepfakes are indistinguishable from reality and truth itself is under attack .
Decoding Life: The Two-Way Mirror of AI and Immunology
The relationship between AI and the immune system is not one-way. While AI helps build digital immunity, it is also revolutionizing the study of human immunology. This creates a powerful feedback loop for innovation.
1. Generative AI Models for T-Cells
At the Institute for Systems Biology, researchers developed TARPON, a generative AI model trained on millions of human T cell receptor sequences. TARPON maps the hypervariable regions of T-cells into a multi-dimensional space, allowing it to generate entirely new, realistic T-cell receptors. This helps scientists understand how the immune system might respond to novel pathogens like COVID-19, revealing why some individuals (particularly older men) suffered worse outcomes due to “rule-breaking” T-cells that blurred the lines between helper and killer functions .
2. The Predictive Immunology Loop
Similarly, the Biohub is working on a “third revolution” in immunology by creating causal data engines. Instead of just describing what cells do, AI models are being built to predict how the immune system will behave. This involves a “Predictive Immunology Loop”: engineer platforms to generate causal data, build AI models to represent that data, and use those models to predict outcomes, which then inspires the generation of new data. This virtuous cycle aims to solve the hardest problems in human immunology, from drug design to preventing inflammation .
3. DNA as Code
Advancements in DNA language models, such as Evo-2, treat the genome as a language to be modeled. Trained on over 9 trillion base pairs, Evo-2 can identify disease-causing mutations and even generate novel biological system designs . This capability has dual-use implications: it can accelerate vaccine development, but it could also be used to design pathogens. To mitigate this, the developers of Evo-2 took the ethical step of excluding pathogens that infect humans from their training data, setting a precedent for safety in AI-driven genomics .
Challenges and the Path to Cyber-Consciousness
Despite the promise, building a true digital immune system is fraught with challenges.
The Black Box Problem: Many AI models are “black boxes.” They can predict with high accuracy but cannot explain why. In high-stakes domains like healthcare or critical infrastructure, we need white-box causal models. We must understand why an AI flagged a specific behavior to trust its autonomous response .
Adversarial AI: Just as defenders use AI, attackers use it to create malware that morphs to avoid detection. The digital immune system must be hardened against tampering, subject to the same red-teaming and zero-trust architecture it is meant to enforce .
Decentralized Governance: As AI agents become more autonomous, we need governance frameworks that keep “humans in the loop.” Blockchain and decentralized protocols are being explored to create immutable logs of AI decisions. This allows for auditability a “black box flight recorder” for AI ensuring that if an AI-driven response causes harm, the chain of events can be traced and accountability can be assigned .
Real-World Implementations
The theoretical benefits of a digital immune system are already being realized in the field:
-
Telecommunications: BT is developing a Network Immune System (NIS) with Ericsson. This system uses reinforcement learning and digital twins of the network to profile how threats might spread. It can autonomously prevent, detect, and respond to cyberattacks in real-time, protecting critical national infrastructure .
-
Financial Services: Major banks use anomaly-detection models to flag fraudulent transactions within milliseconds, protecting millions of customers daily .
-
Cloud Computing: Projects like NebulOuS are embedding AI-based anomaly detectors into Kubernetes clusters operating at the edge, ensuring reliable and secure operations in distributed cloud environments .
Conclusion
The convergence of AI and cybersecurity into a digital immune system marks the next frontier in our relationship with technology. It moves us away from the brittle defenses of the past toward a resilient, adaptive, and intelligent future. By mimicking the elegance of biology from the adaptive immunity of T-cells to the reflex arcs of the nervous system we can build systems capable of protecting themselves.
However, technology alone is not enough. Building a digital immune system requires a cyber-consciousness: a commitment to ethical design, robust governance, and international collaboration . As AI continues to become an extension of our decision-making and identity, our digital immune system must protect not just our data, but our culture, our trust, and our truth. The question is no longer if we will face a cyber crisis, but how intelligently we will fight it. With AI as our immune system, we stand ready to outpace the threats of tomorrow.